Quishing: The Rising QR Code Threat Businesses and Consumers Must Understand

QR codes have become a convenient part of everyday life, but cybercriminals are now exploiting them through a growing threat known as quishing. This form of social engineering hides malicious links inside QR codes delivered through emails, text messages, and even physical advertisements. Learn how quishing attacks work, what warning signs to look for, and the steps businesses and individuals can take to reduce the risk.
AI in 2026: Why Security Must Be the Foundation of the Next Technological Revolution

Artificial Intelligence is no longer experimental. In 2026, it is embedded in business operations, customer experiences, and everyday decision-making. As AI adoption accelerates, security, governance, and responsible use must move from afterthoughts to foundational requirements for organizations and consumers alike.
Most Businesses Don’t Know Their Cyber Risk Until It’s Too Late

This cybersecurity readiness assessment helps organizations understand their current security posture and identify priority areas for improvement.
NIST CSF 2.0 for Small Teams: A 30-Day Quick Start Guide
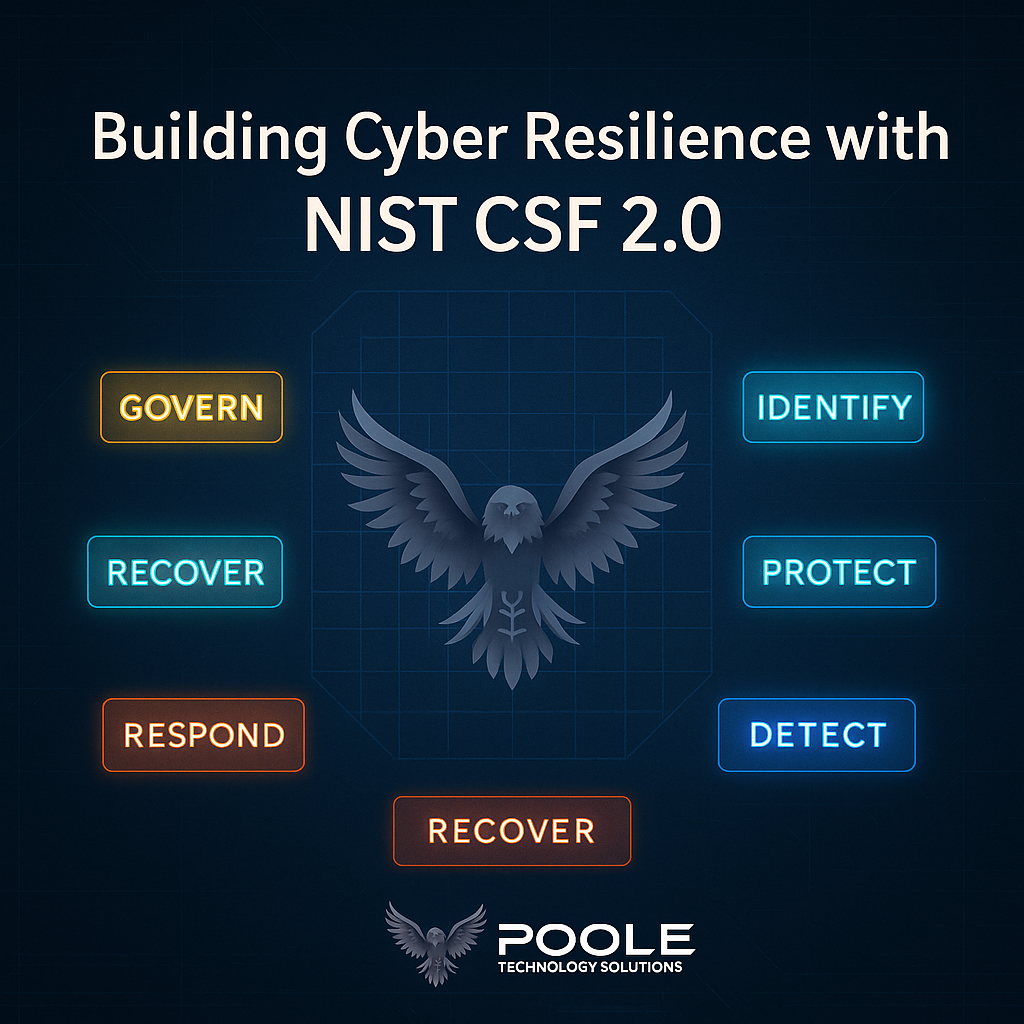
Cybersecurity doesn’t have to be complex to be effective. NIST CSF 2.0 gives small and mid-sized organizations a practical blueprint for identifying risks, protecting systems, and building long-term resilience. In this 30-day quick start, Poole Technology Solutions shows how to turn framework goals into achievable, real-world action.
