AI in 2026: Why Security Must Be the Foundation of the Next Technological Revolution

Artificial Intelligence is no longer experimental. In 2026, it is embedded in business operations, customer experiences, and everyday decision-making. As AI adoption accelerates, security, governance, and responsible use must move from afterthoughts to foundational requirements for organizations and consumers alike.
Most Businesses Don’t Know Their Cyber Risk Until It’s Too Late

This cybersecurity readiness assessment helps organizations understand their current security posture and identify priority areas for improvement.
Cybercriminals Love the Holidays: How to Protect Yourself and Your Business

Holiday scammers take advantage of the busy season by launching targeted email, text, and domain impersonation attacks. From fake delivery alerts to TOAD schemes and look-alike domains, both consumers and businesses face heightened risk. This guide explains the latest threats and practical steps to stay protected during the holidays.
NIST CSF 2.0 for Small Teams: A 30-Day Quick Start Guide
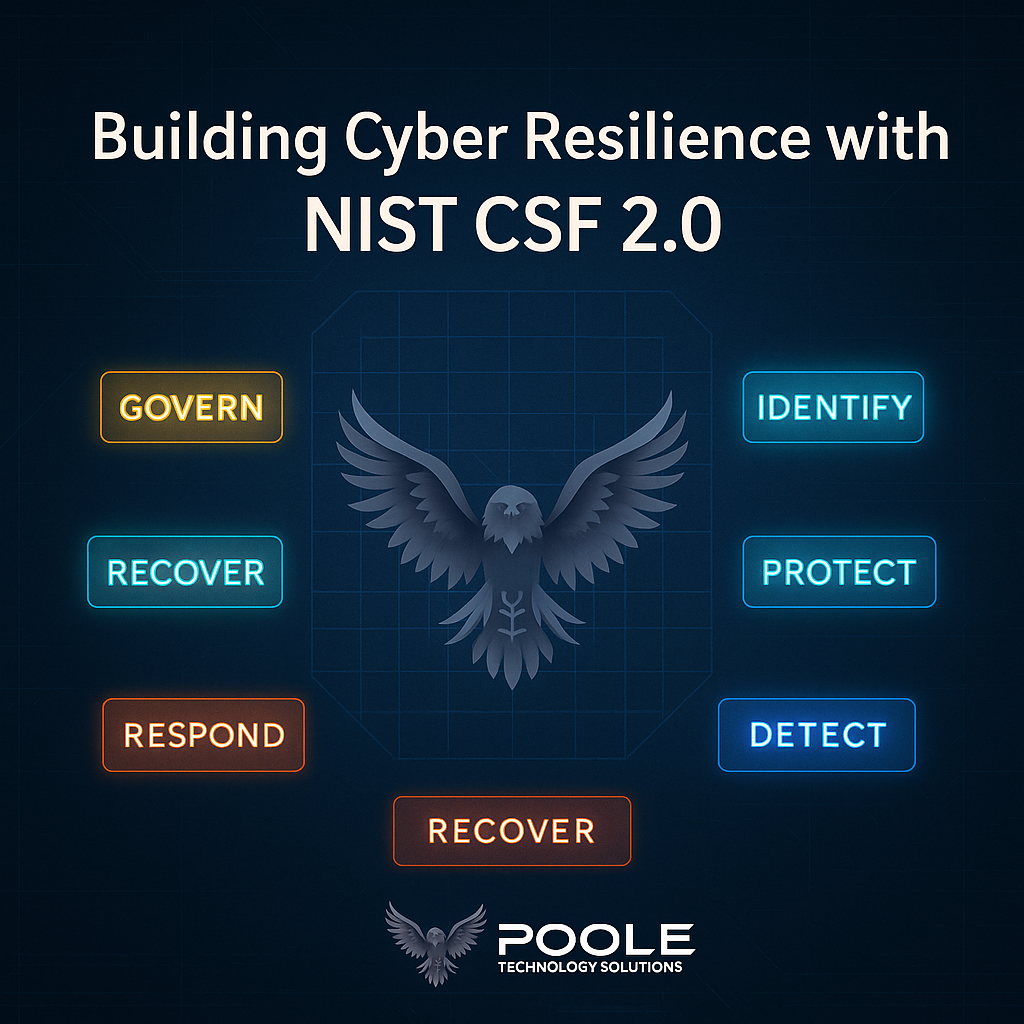
Cybersecurity doesn’t have to be complex to be effective. NIST CSF 2.0 gives small and mid-sized organizations a practical blueprint for identifying risks, protecting systems, and building long-term resilience. In this 30-day quick start, Poole Technology Solutions shows how to turn framework goals into achievable, real-world action.
Fake Quotes, Real Damage: The RFQ Scam Surge in Social Engineering

Think RFQs are just business as usual? Think again. A new wave of phishing campaigns is using fake quote requests to exploit urgency, trust, and human workflow — bypassing traditional defenses. Learn how to spot them and protect your team.
