Introduction
The new NIST Cybersecurity Framework 2.0 (CSF 2.0) is here — and it’s not just for Fortune 500 companies.
While headlines focus on federal agencies and large enterprises, the real opportunity lies with small and mid-sized organizations: those with limited staff, lean budgets, and growing digital footprints that face the same risks as the big players — often with fewer resources to defend against them.
NIST CSF 2.0 gives businesses of all sizes a flexible, outcome-driven structure for improving cybersecurity posture. The challenge? Many small teams struggle to translate the framework’s principles into practical action within their existing workloads.
At Poole Technology Solutions, we help small teams operationalize NIST CSF 2.0 — turning framework guidance into measurable progress. Whether you’re starting from zero or strengthening existing controls, this 30-day quick-start plan is designed to help you build a security foundation that’s realistic, trackable, and aligned to your business goals.
NIST CSF 2.0 in Plain Terms
Released in February 2024, CSF 2.0 modernizes the original 2014 framework to address today’s cloud-first, hybrid, and AI-driven environments. It expands beyond “critical infrastructure” to include all sectors, emphasizing governance, supply-chain risk, and measurable outcomes.
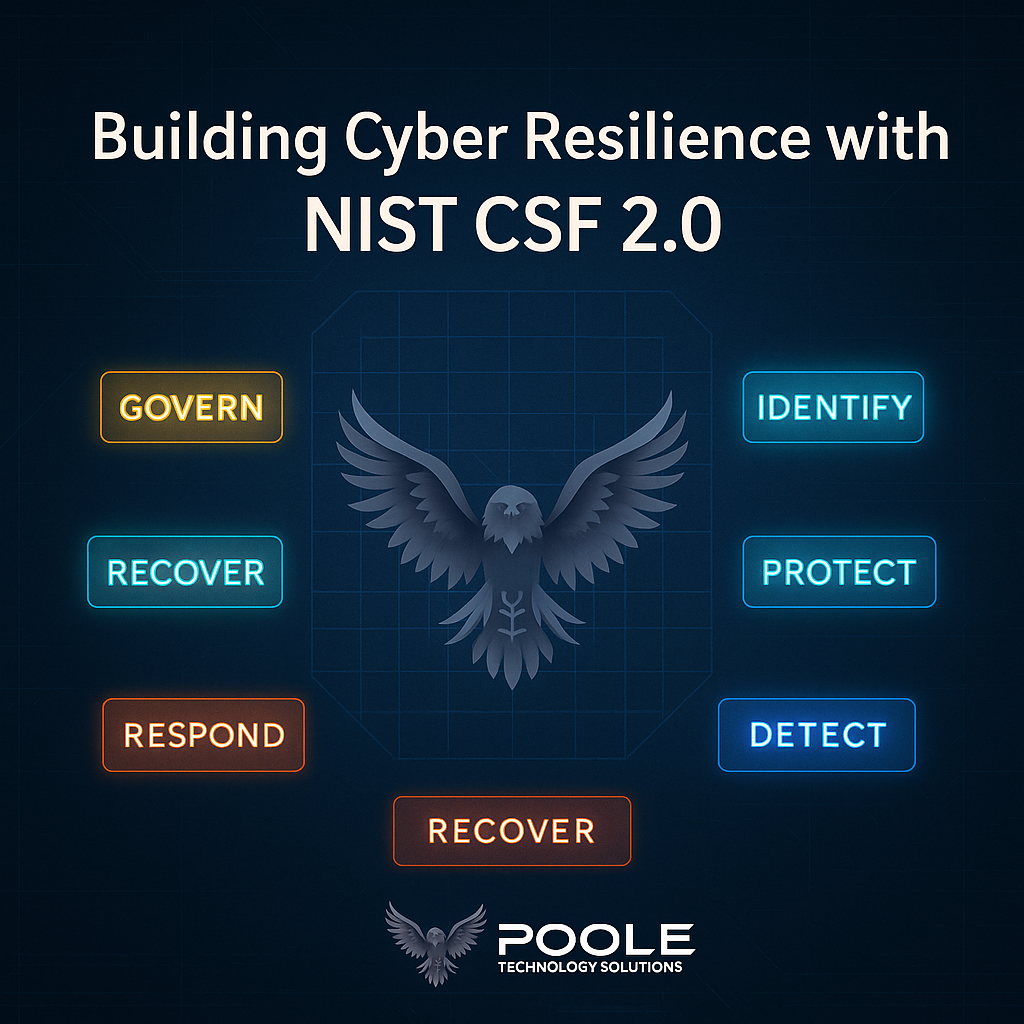
The framework revolves around six core functions:
- Govern (new) – define roles, policies, and accountability.
- Identify – understand assets, risks, and dependencies.
- Protect – implement safeguards like access control and awareness training.
- Detect – monitor systems and identify anomalies.
- Respond – contain and mitigate incidents.
- Recover – restore services and communicate lessons learned.
For small teams, CSF 2.0 serves as a roadmap, not a regulation — helping you prioritize what to do first and prove progress to stakeholders, insurers, or auditors.
The 30-Day Quick-Start Plan
Week 1 – Define and Assess
- Inventory your digital assets (devices, apps, cloud accounts, data repositories).
- Identify business-critical functions and top risks.
- Assign a “cyber lead” or designate responsibility (even part-time).
- Map where you already align to CSF 2.0.
PooleTechSol Tie-In:
We help organizations perform lightweight security posture assessments and build risk registers that align directly with CSF 2.0’s Identify and Govern functions.
Week 2 – Protect and Detect
- Enable multi-factor authentication (MFA) across key platforms.
- Patch and update all systems.
- Implement basic monitoring — even if it’s through existing endpoint tools or cloud logs.
- Conduct a 15-minute staff awareness refresher: phishing, password hygiene, and data handling.
PooleTechSol Tie-In:
Through our Email Security and Awareness Training Services, we integrate Proofpoint-powered safeguards, simulate phishing, and educate staff on real-world threats.
Week 3 – Respond and Recover
- Draft a simple Incident Response Playbook (who does what, when).
- Back up critical data to both cloud and offline storage.
- Test recovery: can you access backups and restore within hours, not days?
PooleTechSol Tie-In:
Our Incident Response Readiness Program provides templates, tabletop exercises, and guidance to ensure small teams can act fast and minimize downtime.
Week 4 – Govern and Improve
- Formalize cybersecurity roles and reporting cadence.
- Review findings and update policies or vendor agreements.
- Plan quarterly security reviews to measure improvement.
- Document everything — it’s your first compliance artifact.
PooleTechSol Tie-In:
We offer vCISO advisory and compliance coaching, helping small teams translate CSF 2.0 into governance metrics for boards, grant applications, or vendor due-diligence packages.
🧰 The 30-Day NIST CSF 2.0 Practical Toolkit
Build measurable progress — one week at a time.
Small teams don’t need binders of policy to improve cybersecurity; they need clarity, momentum, and accountability.
Use this Practical Toolkit from Poole Technology Solutions to track actions, measure readiness, and prove improvement over time.
Quick-Start Checklist
| Week | Focus | Actions | Evidence / Artifacts |
|---|---|---|---|
| Week 1: Define & Assess | Governance + Asset Visibility | • Inventory all assets (devices, SaaS, data) • Identify critical business functions • Assign a cyber lead / owner | – Asset list – Risk register – Responsibility matrix |
| Week 2: Protect & Detect | Controls + Awareness | • Enable MFA everywhere • Patch systems / apps • Launch awareness reminder • Activate basic alerting/logs | – MFA report – Patch schedule – Training attendance list |
| Week 3: Respond & Recover | Incident Readiness | • Draft an IR playbook • Test backup restore • Validate vendor support paths | – IR plan v1 – Backup log – Contact tree |
| Week 4: Govern & Improve | Measurement + Policy | • Review results • Update policies • Plan quarterly reviews • Present summary to leadership | – CSF 2.0 summary deck – Updated SOPs – Executive report |
Need help jump-starting your checklist?
Poole Technology Solutions offers a CSF 2.0 Readiness Package — including templates, 1-hour consultation, and a tailored improvement roadmap.
📊 Readiness Scorecard (Self-Assessment)
Score each category from 1 = Not Started to 5 = Fully Implemented
| CSF 2.0 Function | Score (1-5) | Notes / Next Step |
|---|---|---|
| Govern | e.g., Defined security roles & oversight? | |
| Identify | Asset inventory complete and current? | |
| Protect | MFA, patching, training applied? | |
| Detect | Monitoring/logging in place? | |
| Respond | IR plan tested this quarter? | |
| Recover | Backup validated and recovery tested? |
How to Use It:
- Average your six scores.
- Anything below 3 is a priority area for next quarter.
- Repeat every 90 days to visualize improvement and show progress to management or auditors.
PooleTechSol Tie-In:
Clients who complete this scorecard with us receive a personalized Risk Maturity Snapshot and a 30-minute advisory session outlining top-three priorities mapped to NIST CSF 2.0.
Why This Matters
For small organizations, the hardest part of cybersecurity isn’t the technology — it’s the translation between strategy and execution.
CSF 2.0 helps bridge that gap, and with the right partner, you can move from reactive to proactive security in just a month of disciplined effort.
At Poole Technology Solutions, our mission is simple: to make enterprise-grade cybersecurity accessible, actionable, and affordable for growing businesses.
Conclusion
You don’t need a 50-person security team to implement NIST CSF 2.0 — you just need a plan, clear priorities, and consistent follow-through.
In 30 days, small teams can establish visibility, define accountability, and adopt repeatable security habits that scale as they grow.
If you’re ready to assess your posture, align with CSF 2.0, or strengthen your existing controls, Poole Technology Solutions can help you start today — one practical step at a time.
Always Improving™ — because better security starts with better focus.